Security Overlay Assessments – Common Findings & Why They Matter
At Contextual Security Solutions, we have all the bread and butter compliance assessments that you would expect today: PCI, HIPAA, CIS, and NIST to name a few. We love evaluating organizations on them and helping give a clear picture of where they stand and even how they measure up within a vertical. There are many limitations to frameworks, and those limitations go beyond the scope of this paper. However, there is one that bears addressing here. The intent of frameworks is to evaluate organizational security posture from one angle or another. One important element that this misses is the security posture of many Security Overlays within an organization’s network.
What is a Security Overlay?
For those that are unaware of the term, security overlays are essentially security controls (software, hardware etc.) that provide protection over various area’s within organization networks. Anti-Malware, logging and monitoring, backup solutions, and firewalls are all examples of traditional Security Overlays. Overlays often are called out in compliance frameworks: Requirement 5 for Anti-Malware protections (PCI) and Control 13 for Network Monitoring and Defense (CIS), to name a few. But all frameworks don’t cover all security overlays. Some frameworks miss, or don’t address certain overlay types altogether. So what does that mean for overlays that aren’t part of the organization’s chosen compliance framework? At best, the organization still carefully watches all aspects of that overlay and knows how to optimize it. At worst, core security considerations for the overlay are missed, resulting in a poorly optimized, or even insecure overlay and a weaker overall security posture.
Enter the Security Overlay Assessment
Rather than looking at the problem from the framework level, which many organizations have to anyway, we flipped the script and started looking at the overlays themselves. What we have found working with clients in this way is that there are a whole host of areas that are often overlooked by organizations across verticals. We have been performing these audits for several years and here are a few that we’ve seen.
Backups – Protection Through Segmentation
Backup solutions are called out in many compliance frameworks. I won’t bore you with listing them all. However, the way the backup solution is configured, especially as regards authentication, is a core component of protecting a solution that protects you in case of lost data. The single most common and concerning element I see with backup solutions is that they reside on the same domain and are authenticated with the same credentials as the primary host domain with no multi-factor solution in place. Sure, it sounds convenient to be able to log into your backup solution with the same credentials as the admin account you use for everything else, but that’s exactly what the bad guy is going to say when you finally have that fated compromise. If it’s a silent and persistent actor, they would be only too happy to hop over to your backup solution, drop their favorite ransomware, and then wait for the timeline to run out on your backup jobs. I see this in so many organizations, but you won’t see it in any of the top frameworks today. It’s also not a one-and-done solution. No security is, but having separate domains with multiple layers of security is definitely going to put some brakes on the average bad actor.
Logging – Is It done? Are They Reviewed? Are They Watched?
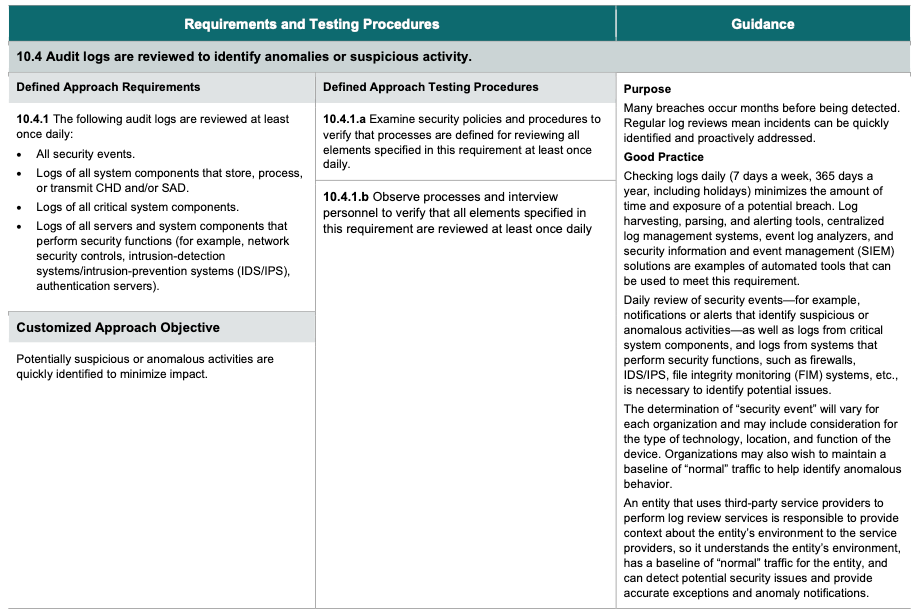
Logging is also mentioned in almost every compliance framework. However, logging is often only required for a subset of security overlays (with PCI having some of the most stringent logging requirements for those overlays). What happens when you are not a shop that is required to be PCI compliant above an Self-Assessment-Questionnaire (SAQ) level? Then how many overlays are logging data? For how long? Are they logging to a Security Information and Event Management (SIEM) system? Most organizations are not able to respond to every alert that comes in. Are your overlays setup to alert you of any suspected issues, or better yet, aggregate to the SIEM and have it augment your workforce through alerting and decision making? So often, I see administrators strapped for work because they have twenty overlays, some logging and some alerting and maybe none aggregating and trimmed to make informed decisions. This leads to alert fatigue, missed events, and ultimately compromises. While frameworks have logging and alerting controls in place designed to protect against this, many overlays will still fall through the cracks and ultimately legitimate issues will too.
Multi-Factor-All-The-Things
Finally, something that I see in so many overlay reviews is a single factor of authentication (usually an administrator password), or even a shared account, to log into an overlay system on a client network. Sure, PCI, CIS, and several frameworks call out the need for multi-factor-authentication (MFA) on various in-scope segments and elements, but I could write books with the amount of times I’ve seen critical security overlays, overlays that could give privileged access or some powerful lateral movement, without any additional layers of authentication protection.
Where Do We Go From Here?
You can’t defend what you don’t know. Security Overlay Assessments are designed to take a deep dive into your security posture from an angle that is seldom reviewed. We aim to give you visibility into an area that we know you will get value from.