Web TLS certificates provide critical protections for web traffic. Encryption of session and transport data is key to ensuring millions of people who browse the web daily can do so without fear of losing their sensitive data. However, attacks on cryptography are always evolving. A TLS certificate that sits out in the wild poses a continued risk, just due to online “shelf-life.” If a bad actor has a year to work against a certificate with evolving technology, the risk only grows from day-to-day.
What happens now?
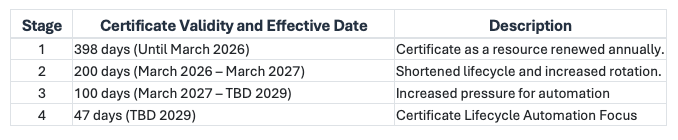
The CA/Browser Forum (CAB) has voted on an evolution of plans to shrink the window. For reference, here is a table:
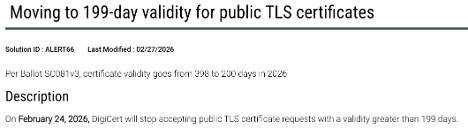
In addition, you can find significantly more detail than this on the CAB’s latest baseline requirements page. This means administrators will have to, at the very least, log into their CA and generate new certificates on a more frequent pace to remain valid by the CA. You can see this in recent blog posts by popular CA’s like Digicert:
Where is this going?
The trend of the CAB is looking to shift focus to more frequent certificate changes. As the landscape of transmission security changes (more attacker tools and powerful hardware), the need for automated solutions to replace traditional human-driven repeatable methods becomes clear. In the next couple of years, we might even see “certificate-renewal-as-a-service” become a thing, or major providers offering similar options on their platforms.
What does it mean?
If you are responsible for managing digital certificates for your organization, you will want to pay attention here. In just 3 short years, certificates will see an almost 10x reduction in lifespan. This means not only that the certificate itself will need to be replaced to be considered valid (obviously), but relevant compliance frameworks that you adhere to will require it for transmission controls. PCI DSS Requirement 4.2 states:
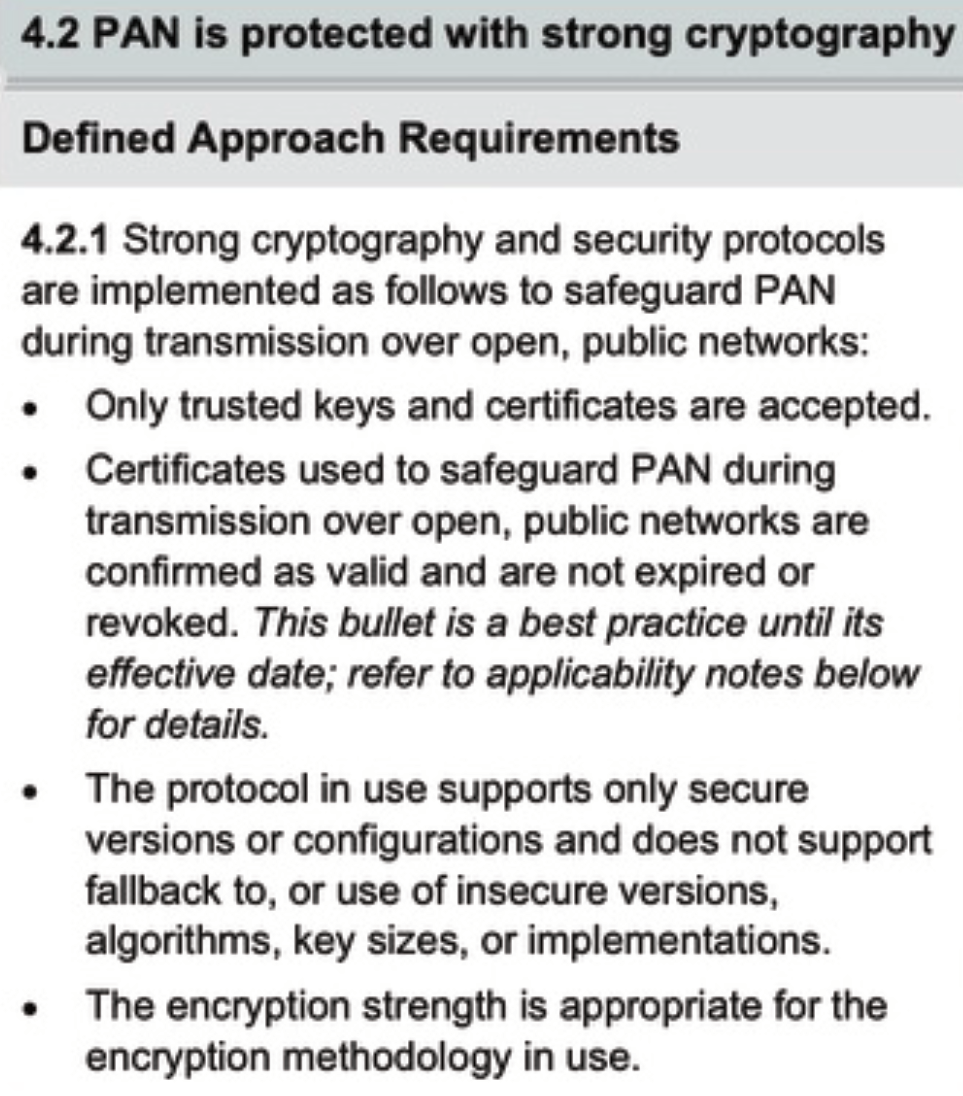
Notice bullet 2. As of the March 31, 2025 effective date, merchants responsible for transmitting cardholder data must account for these changes, and should be prepared to demonstrate increased changes to maintain compliance per PCI DSS requirement 4.2. Now is the time to begin looking through what you own and what your Third Party Service Providers own with respect to data transmission. Remember, this 200-day change is just a part of a transition to a process that will change fundamentals of certificate management. Let us talk with you today about options moving forward, both for compliance, and security planning.